Technology news, features and articles
Throughout history, the pursuit of technology to help us work harder, faster and more safely has led to some truly incredible inventions that have changed the world we live in — from the ancient tools first used by our ancestors to 21st-century breakthroughs such as bionic eyes and artificial intelligence (AI). Our expert writers and editors address the groundbreaking developments in robotics, quantum computing and much more with the latest future technology news, articles and features.
Editor's Picks
Latest about Technology
-
-
 'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published
'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published -
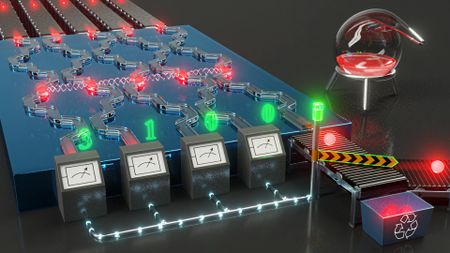
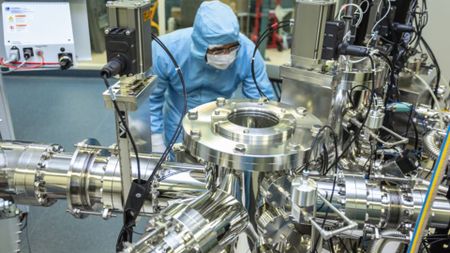
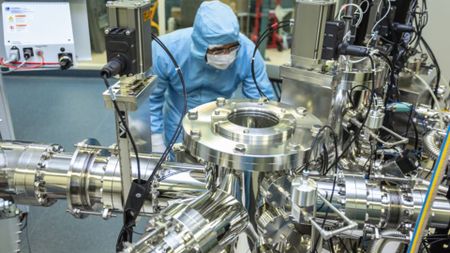
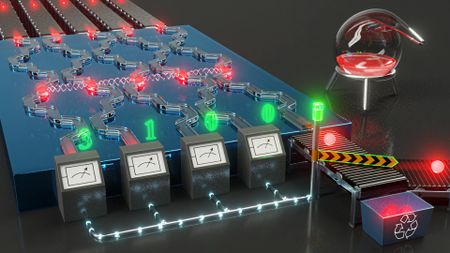
 Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published
Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published -
 New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published
New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published -
 Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published
Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published -
 Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published
Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published -
 Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published
Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published
-
Explore Technology
Artificial Intelligence
-
-
 'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published
'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published -
 Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published
Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published -
 'I violated every principle I was given': AI agent deletes company's entire database in 9 seconds, then confessesBy Kenna Hughes-Castleberry Published
'I violated every principle I was given': AI agent deletes company's entire database in 9 seconds, then confessesBy Kenna Hughes-Castleberry Published -
 How everything you do is being monitored in an AI-fuelled 'surveillance capitalism system' that's ramping up aggressivelyBy Anne Toomey McKenna Published
How everything you do is being monitored in an AI-fuelled 'surveillance capitalism system' that's ramping up aggressivelyBy Anne Toomey McKenna Published -
 Claude Mythos explained: Is Anthropic's most powerful AI model really too dangerous to release to the public?By Carly Page Published
Claude Mythos explained: Is Anthropic's most powerful AI model really too dangerous to release to the public?By Carly Page Published -
 Scientists build specialist 'AGI processor' that they believe will power the next wave of AI agentsBy Roland Moore-Colyer Published
Scientists build specialist 'AGI processor' that they believe will power the next wave of AI agentsBy Roland Moore-Colyer Published -
 Book'We're the best servants anyone could dream of!': AI superintelligence has no need to enslave humans because we're already bowing to itBy Gregory Stock Published
Book'We're the best servants anyone could dream of!': AI superintelligence has no need to enslave humans because we're already bowing to itBy Gregory Stock Published -
 Hackers used AI to steal hundreds of millions of Mexican government and private citizen records in one of the largest cybersecurity breaches everBy Kenna Hughes-Castleberry Published
Hackers used AI to steal hundreds of millions of Mexican government and private citizen records in one of the largest cybersecurity breaches everBy Kenna Hughes-Castleberry Published -
 AI for breakup texts? How 'sycophantic' chatbots are messing with our ability to handle difficult social situations.By Roland Moore-Colyer Published
AI for breakup texts? How 'sycophantic' chatbots are messing with our ability to handle difficult social situations.By Roland Moore-Colyer Published
-
Communications
-
-
 Could there ever be a worldwide internet outage?By Abby Wilson Published
Could there ever be a worldwide internet outage?By Abby Wilson Published -
 Science history: First computer-to-computer message lays the foundation for the internet, but it crashes halfway through — Oct. 29, 1969By Tia Ghose Published
Science history: First computer-to-computer message lays the foundation for the internet, but it crashes halfway through — Oct. 29, 1969By Tia Ghose Published -
 Science historyScience history: First two-way phone call across outdoor lines made by Alexander Graham Bell — Oct. 9, 1876By Tia Ghose Published
Science historyScience history: First two-way phone call across outdoor lines made by Alexander Graham Bell — Oct. 9, 1876By Tia Ghose Published -
 Scientists invent 'Pulse-Fi' prototype — a Wi-Fi heart rate monitor that's cheaper to set up than the best wearable devicesBy Sophie Berdugo Published
Scientists invent 'Pulse-Fi' prototype — a Wi-Fi heart rate monitor that's cheaper to set up than the best wearable devicesBy Sophie Berdugo Published -
 Scientists develop 'full-spectrum' 6G chip that could transfer data at 100 gigabits per second — 10,000 times faster than 5GBy Rich McEachran Published
Scientists develop 'full-spectrum' 6G chip that could transfer data at 100 gigabits per second — 10,000 times faster than 5GBy Rich McEachran Published -
 Google has turned 2 billion smartphones into a global earthquake warning system — it's as effective as seismometers, tests showBy Ben Turner Published
Google has turned 2 billion smartphones into a global earthquake warning system — it's as effective as seismometers, tests showBy Ben Turner Published -
 Japan sets new internet speed record — it's 4 million times faster than average US broadband speedsBy Perri Thaler Published
Japan sets new internet speed record — it's 4 million times faster than average US broadband speedsBy Perri Thaler Published -
 Your data is being compromised much quicker than ever before, but you don't have to sit still and take itBy Mike Chapple Published
Your data is being compromised much quicker than ever before, but you don't have to sit still and take itBy Mike Chapple Published -
 New 'super laser' amplifier could make the internet 10 times fasterBy Peter Ray Allison Last updated
New 'super laser' amplifier could make the internet 10 times fasterBy Peter Ray Allison Last updated
-
Computing
-
-
 Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published
Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published -
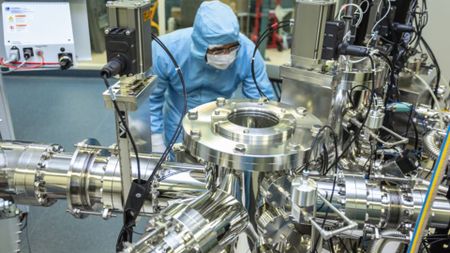
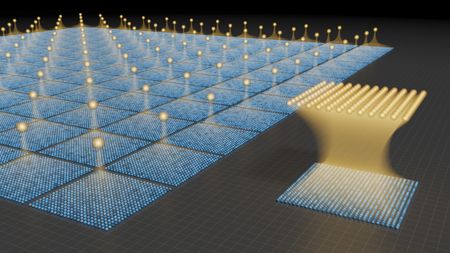
 Breakthrough in experimental light-powered quantum computers could mean scaling them up is now far more viableBy Tristan Greene Published
Breakthrough in experimental light-powered quantum computers could mean scaling them up is now far more viableBy Tristan Greene Published -
 New data center will be partially powered by human brain cells for the first timeBy Carly Page Published
New data center will be partially powered by human brain cells for the first timeBy Carly Page Published -
 Scientists create new type of encryption that protects video files against quantum computing attacksBy Carly Page Published
Scientists create new type of encryption that protects video files against quantum computing attacksBy Carly Page Published -
 IBM quantum processor achieves highest fidelity calculations for the longest period of time on recordBy Tristan Greene Published
IBM quantum processor achieves highest fidelity calculations for the longest period of time on recordBy Tristan Greene Published -
 Quantum computers need just 10,000 qubits — not the millions we assumed — to break the world's most secure encryption algorithmsBy Keumars Afifi-Sabet Published
Quantum computers need just 10,000 qubits — not the millions we assumed — to break the world's most secure encryption algorithmsBy Keumars Afifi-Sabet Published -
 Is the metaverse finally dead and buried? What's really going on with the embattled idea of living in virtual worlds.By Drew Turney Published
Is the metaverse finally dead and buried? What's really going on with the embattled idea of living in virtual worlds.By Drew Turney Published -
 Computing quiz: Can you match these 'ancient' devices to their pictures?By Kenna Hughes-Castleberry Published
Computing quiz: Can you match these 'ancient' devices to their pictures?By Kenna Hughes-Castleberry Published -
 World's smallest QR code can store data for thousands of years — but you need an electron microscope to see itBy Fiona Jackson Published
World's smallest QR code can store data for thousands of years — but you need an electron microscope to see itBy Fiona Jackson Published
-
Electric Vehicles
-
-
 The first flying taxis could start operating in 2026 — will this new form of transport actually take off?By Edd Gent Published
The first flying taxis could start operating in 2026 — will this new form of transport actually take off?By Edd Gent Published -
 Meet Sky Dragon, the giant 10-person 'flying taxi' that just passed its first flight test in ChinaBy Alan Bradley Published
Meet Sky Dragon, the giant 10-person 'flying taxi' that just passed its first flight test in ChinaBy Alan Bradley Published -
 China puts a sodium-ion battery into an EV for the first time — it can drive 248 miles on a single chargeBy Rory Bathgate Published
China puts a sodium-ion battery into an EV for the first time — it can drive 248 miles on a single chargeBy Rory Bathgate Published -
 Sodium-ion batteries are getting ready for prime time. How can they improve EVs?By Rory Bathgate Published
Sodium-ion batteries are getting ready for prime time. How can they improve EVs?By Rory Bathgate Published -
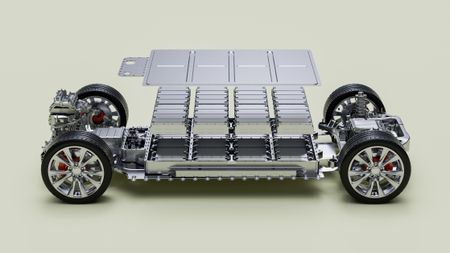 Chinese EV maker claims it's engineered the world’s first semi-solid-state EV battery with huge 620-mile rangeBy Alan Bradley Published
Chinese EV maker claims it's engineered the world’s first semi-solid-state EV battery with huge 620-mile rangeBy Alan Bradley Published -
 New EV motor invention could cut 1,000 pounds from future vehicles, making them much lighter while boosting their rangeBy Alan Bradley Published
New EV motor invention could cut 1,000 pounds from future vehicles, making them much lighter while boosting their rangeBy Alan Bradley Published -
 Scientists create new solid-state sodium-ion battery — they say it'll make EVs cheaper and saferBy Rory Bathgate Published
Scientists create new solid-state sodium-ion battery — they say it'll make EVs cheaper and saferBy Rory Bathgate Published -
 Watch four flying cars go toe-to-toe in new 'Formula One of the skies'By Damien Pine Published
Watch four flying cars go toe-to-toe in new 'Formula One of the skies'By Damien Pine Published -
 Toyota to launch world's first EV with a solid-state battery by 2027 — they're expected to last longer and charge fasterBy Skyler Ware Published
Toyota to launch world's first EV with a solid-state battery by 2027 — they're expected to last longer and charge fasterBy Skyler Ware Published
-
Engineering
-
-
 New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published
New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published -
 Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published
Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published -
 We went to Finland to hear about the new 'sand battery' that will turn stored renewable energy back into power for the electrical gridBy Sophie Berdugo Published
We went to Finland to hear about the new 'sand battery' that will turn stored renewable energy back into power for the electrical gridBy Sophie Berdugo Published -
 China launches world first 'megawatt-class wind power airship'By Rory Bathgate Published
China launches world first 'megawatt-class wind power airship'By Rory Bathgate Published -
 Days numbered for 'risky' lithium-ion batteries, scientists say, after fast-charging breakthrough in sodium-ion alternativeBy Rory Bathgate Published
Days numbered for 'risky' lithium-ion batteries, scientists say, after fast-charging breakthrough in sodium-ion alternativeBy Rory Bathgate Published -
 Japan trials 100-kilowatt laser weapon — it can cut through metal and drones mid-flightBy Fiona Jackson Published
Japan trials 100-kilowatt laser weapon — it can cut through metal and drones mid-flightBy Fiona Jackson Published -
 MIT invention uses ultrasound to shake drinking water out of the air, even in dry regionsBy Owen Hughes Published
MIT invention uses ultrasound to shake drinking water out of the air, even in dry regionsBy Owen Hughes Published -
 NASA’s ultraquiet supersonic 'flying swordfish' makes history with first test flightBy Damien Pine Published
NASA’s ultraquiet supersonic 'flying swordfish' makes history with first test flightBy Damien Pine Published -
 Science history: The Tacoma Narrows Bridge collapses, forcing a complete rethink in structural engineering — Nov. 7, 1940By Tia Ghose Published
Science history: The Tacoma Narrows Bridge collapses, forcing a complete rethink in structural engineering — Nov. 7, 1940By Tia Ghose Published
-
Robotics
-
-
 Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published
Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published -
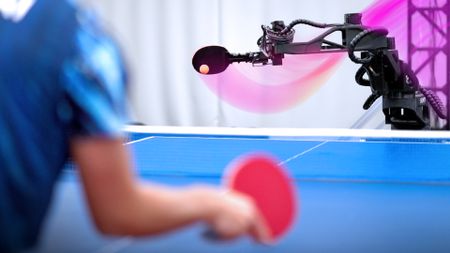 Advanced AI-powered table-tennis-playing robot can match up to the professionals — watch it in actionBy Kenna Hughes-Castleberry Published
Advanced AI-powered table-tennis-playing robot can match up to the professionals — watch it in actionBy Kenna Hughes-Castleberry Published -
 This humanoid robot does all your housework for you — and its makers say it's ready for your homeBy Kenna Hughes-Castleberry Published
This humanoid robot does all your housework for you — and its makers say it's ready for your homeBy Kenna Hughes-Castleberry Published -
 AI compressed billions of years of evolution into seconds to create 'Lego-like robots' that can recover even when they lose limbsBy Alan Bradley Published
AI compressed billions of years of evolution into seconds to create 'Lego-like robots' that can recover even when they lose limbsBy Alan Bradley Published -
 Humanoid robots show off creepily impressive kung-fu moves during Lunar New Year festival in ChinaBy Keumars Afifi-Sabet Published
Humanoid robots show off creepily impressive kung-fu moves during Lunar New Year festival in ChinaBy Keumars Afifi-Sabet Published -
 Watch awkward Chinese humanoid robot lay it all down on the dance floorBy Alan Bradley Published
Watch awkward Chinese humanoid robot lay it all down on the dance floorBy Alan Bradley Published -
 Drones could achieve 'infinite flight' after engineers create laser-based wireless power system that charges them from the groundBy Alan Bradley Published
Drones could achieve 'infinite flight' after engineers create laser-based wireless power system that charges them from the groundBy Alan Bradley Published -
 Creepy humanoid robot face learned to move its lips more accurately by staring at itself in the mirror, then watching YouTubeBy Fiona Jackson Published
Creepy humanoid robot face learned to move its lips more accurately by staring at itself in the mirror, then watching YouTubeBy Fiona Jackson Published -
 Why the rise of humanoid robots could make us less comfortable with each otherBy Berry Billingsley Published
Why the rise of humanoid robots could make us less comfortable with each otherBy Berry Billingsley Published
-
More about Technology
-
-
 'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published
'Feuding tech bros' go head to head in legal showdown. But what does it mean for the future of AI?By Rob Nicholls Published -
 Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published
Live 'quantum network' being tested in New York — overcoming key hurdles could bring us closer to an 'unhackable' internetBy Alan Bradley Published -
 New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published
New water battery could last until the 24th century — and it can be safely discarded in the environmentBy Rory Bathgate Published -
 Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published
Quantum battery charges in a quadrillionth of a second with a laser — larger prototypes could last for years after charging for just a minuteBy Rory Bathgate Published -
 Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published
Google AI breakthrough means chatbots use six times less memory during conversations without compromising performanceBy Fiona Jackson Published -
 Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published
Humanoid robots have outpaced human runners in the half-marathon, beating the world record — here are the secrets to this astonishing featBy Alan Bradley Published -
 'I violated every principle I was given': AI agent deletes company's entire database in 9 seconds, then confessesBy Kenna Hughes-Castleberry Published
'I violated every principle I was given': AI agent deletes company's entire database in 9 seconds, then confessesBy Kenna Hughes-Castleberry Published -
 Breakthrough in experimental light-powered quantum computers could mean scaling them up is now far more viableBy Tristan Greene Published
Breakthrough in experimental light-powered quantum computers could mean scaling them up is now far more viableBy Tristan Greene Published -
 New data center will be partially powered by human brain cells for the first timeBy Carly Page Published
New data center will be partially powered by human brain cells for the first timeBy Carly Page Published -
 How everything you do is being monitored in an AI-fuelled 'surveillance capitalism system' that's ramping up aggressivelyBy Anne Toomey McKenna Published
How everything you do is being monitored in an AI-fuelled 'surveillance capitalism system' that's ramping up aggressivelyBy Anne Toomey McKenna Published
-

 Live Science Plus
Live Science Plus












