Technology news, features and articles
Throughout history, the pursuit of technology to help us work harder, faster and more safely has led to some truly incredible inventions that have changed the world we live in — from the ancient tools first used by our ancestors to 21st-century breakthroughs such as bionic eyes and artificial intelligence (AI). Our expert writers and editors address the groundbreaking developments in robotics, quantum computing and much more with the latest future technology news, articles and features.
Latest about Technology
-
-

New AI image generator runs using 10 times fewer steps than today's best models — and it's coming to smartphones and laptops
By Carly Page Published -

GPS is being weaponized in electronic warfare — and it's putting ships at risk
By Anna Raymaker Published -

Reading AI summaries makes people more likely to buy something — despite alarming 60% hallucination rate
By Drew Turney Published -
What's the biggest bottleneck to building better AI? It's no longer the lack of computing resources — it's generating enough energy to feed it
By Carly Page Published -
AI hallucinations work both ways, study shows — using chatbots can amplify and reinforce our own delusions
By Peter Ray Allison Published -

Meet Sky Dragon, the giant 10-person 'flying taxi' that just passed its first flight test in China
By Alan Bradley Published -
World's smallest QR code can store data for thousands of years — but you need an electron microscope to see it
By Fiona Jackson Published
-
Explore Technology
Artificial Intelligence
-
-

New AI image generator runs using 10 times fewer steps than today's best models — and it's coming to smartphones and laptops
By Carly Page Published -

Reading AI summaries makes people more likely to buy something — despite alarming 60% hallucination rate
By Drew Turney Published -
What's the biggest bottleneck to building better AI? It's no longer the lack of computing resources — it's generating enough energy to feed it
By Carly Page Published -
AI hallucinations work both ways, study shows — using chatbots can amplify and reinforce our own delusions
By Peter Ray Allison Published -

Humans are being replaced by machines in the food supply chain — and it's leading to truckloads of waste
By Mohammed F. Alzuhair Published -
Anthropic collides with the Pentagon over AI safety — here's everything you need to know
By Deni Ellis Béchard Published -
Scientists made AI agents ruder — and they performed better at complex reasoning tasks
By Drew Turney Published -

Acing this new AI exam — which its creators say is the toughest in the world — might point to the first signs of AGI
By Tristan Greene Published -
Your own voice could be your biggest privacy threat. How can we stop AI technologies exploiting it?
By Drew Turney Published
-
Communications
-
-

Could there ever be a worldwide internet outage?
By Abby Wilson Published -
 Deals
DealsStream David Attenborough's Great Barrier Reef and many more nature documentaries with a 77% saving in this Paramount+ Black Friday deal
By Paul Brett Published -
 Deals
DealsGet a host of brilliant science documentaries at your fingertips with Paramount Plus starting at just $2.99 a month
By Rich Owen Published -

Science history: First computer-to-computer message lays the foundation for the internet, but it crashes halfway through — Oct. 29, 1969
By Tia Ghose Published -
 Science history
Science historyScience history: First two-way phone call across outdoor lines made by Alexander Graham Bell — Oct. 9, 1876
By Tia Ghose Published -

Scientists invent 'Pulse-Fi' prototype — a Wi-Fi heart rate monitor that's cheaper to set up than the best wearable devices
By Sophie Berdugo Published -

Scientists develop 'full-spectrum' 6G chip that could transfer data at 100 gigabits per second — 10,000 times faster than 5G
By Rich McEachran Published -

Google has turned 2 billion smartphones into a global earthquake warning system — it's as effective as seismometers, tests show
By Ben Turner Published -

Japan sets new internet speed record — it's 4 million times faster than average US broadband speeds
By Perri Thaler Published
-
Computing
-
-
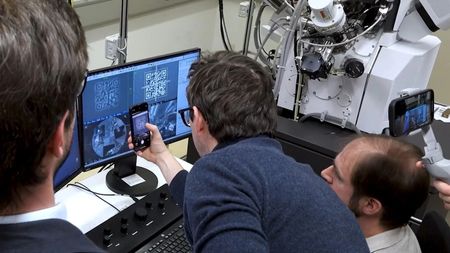
World's smallest QR code can store data for thousands of years — but you need an electron microscope to see it
By Fiona Jackson Published -

Meet the world's smallest AI supercomputer — it packs 'doctorate-level intelligence', its makers say, and can fit into your pocket
By Alan Bradley Published -
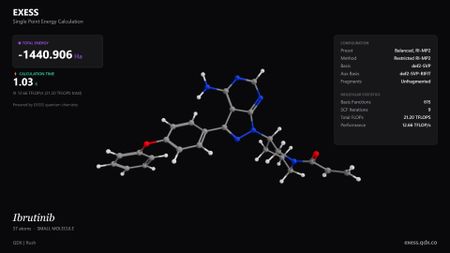
Ultrafast quantum chemistry engine could speed up the development of new medicines and materials
By Skyler Ware Published -
'Thermodynamic computer' can mimic AI neural networks — using orders of magnitude less energy to generate images
By Anna Demming Published -
Microsoft can now store data for 10,000 years on everyday glass thanks to laser breakthrough
By Keumars Afifi-Sabet Published -
MIT designs computing component that uses waste heat 'as a form of information'
By Owen Hughes Published -

Google Glass has found yet another lease of life — but is it too little too late for smart glasses?
By Max L Wilson Published -
Tapping into new 'probabilistic computing' paradigm can make AI chips use much less power, scientists say
By Fiona Jackson Published -

MIT's chip stacking breakthrough could cut energy use in power-hungry AI processes
By Fiona Jackson Published
-
Electric Vehicles
-
-

Meet Sky Dragon, the giant 10-person 'flying taxi' that just passed its first flight test in China
By Alan Bradley Published -

China puts a sodium-ion battery into an EV for the first time — it can drive 248 miles on a single charge
By Rory Bathgate Published -

Sodium-ion batteries are getting ready for prime time. How can they improve EVs?
By Rory Bathgate Published -
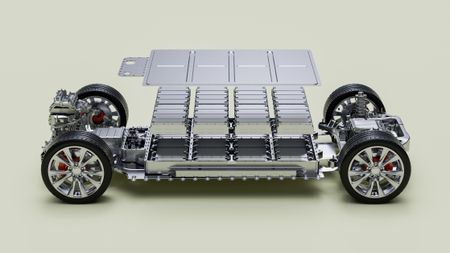
Chinese EV maker claims it's engineered the world’s first semi-solid-state EV battery with huge 620-mile range
By Alan Bradley Published -

New EV motor invention could cut 1,000 pounds from future vehicles, making them much lighter while boosting their range
By Alan Bradley Published -
Scientists create new solid-state sodium-ion battery — they say it'll make EVs cheaper and safer
By Rory Bathgate Published -

Watch four flying cars go toe-to-toe in new 'Formula One of the skies'
By Damien Pine Published -

Toyota to launch world's first EV with a solid-state battery by 2027 — they're expected to last longer and charge faster
By Skyler Ware Published -

New hydrogen battery can operate four times colder than before — meaning denser and longer-lasting EV batteries
By Roland Moore-Colyer Published
-
Engineering
-
-

China launches world first 'megawatt-class wind power airship'
By Rory Bathgate Published -

Days numbered for 'risky' lithium-ion batteries, scientists say, after fast-charging breakthrough in sodium-ion alternative
By Rory Bathgate Published -

Japan trials 100-kilowatt laser weapon — it can cut through metal and drones mid-flight
By Fiona Jackson Published -

MIT invention uses ultrasound to shake drinking water out of the air, even in dry regions
By Owen Hughes Published -

NASA’s ultraquiet supersonic 'flying swordfish' makes history with first test flight
By Damien Pine Published -

Science history: The Tacoma Narrows Bridge collapses, forcing a complete rethink in structural engineering — Nov. 7, 1940
By Tia Ghose Published -

China's new 'solar-power window coating' can capture energy and power household devices
By Peter Ray Allison Published -

A scalding hot 'sand battery' is now heating a small Finnish town
By Sophie Berdugo Published -

Secretive X37-B space plane to test quantum navigation system — scientists hope it will one day replace GPS
By Samuel Lellouch Published
-
Robotics
-
-

Humanoid robots show off creepily impressive kung-fu moves during Lunar New Year festival in China
By Keumars Afifi-Sabet Published -

Watch awkward Chinese humanoid robot lay it all down on the dance floor
By Alan Bradley Published -

Drones could achieve 'infinite flight' after engineers create laser-based wireless power system that charges them from the ground
By Alan Bradley Published -

Creepy humanoid robot face learned to move its lips more accurately by staring at itself in the mirror, then watching YouTube
By Fiona Jackson Published -

Why the rise of humanoid robots could make us less comfortable with each other
By Berry Billingsley Published -
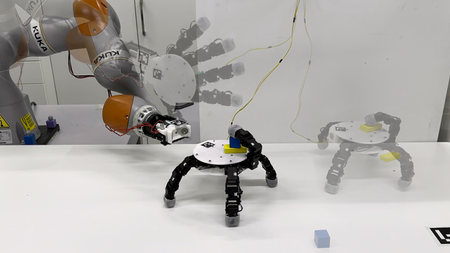
Creepy robotic hand detaches at the wrist before scurrying away to collect objects
By Owen Hughes Published -
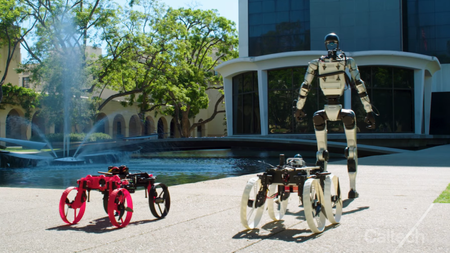
New 'Transformer' humanoid robot can launch a shapeshifting drone off its back — watch it in action
By Bobby Hellard Published -

Bizarre robotic chair concept looks like a crab and can carry you around the house — it can even help you into your car
By Alan Bradley Published -

Watch: Chinese company's new humanoid robot moves so smoothly, they had to cut it open to prove a person wasn't hiding inside
By Owen Hughes Published
-
More about Technology
-
-
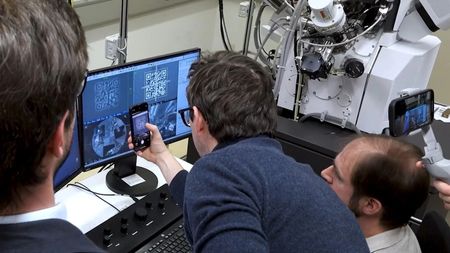
World's smallest QR code can store data for thousands of years — but you need an electron microscope to see it
By Fiona Jackson Published -

Humans are being replaced by machines in the food supply chain — and it's leading to truckloads of waste
By Mohammed F. Alzuhair Published -
Anthropic collides with the Pentagon over AI safety — here's everything you need to know
By Deni Ellis Béchard Published
-
 Live Science Plus
Live Science Plus