Record-Setting Spam Effort Turns Computers into Zombies
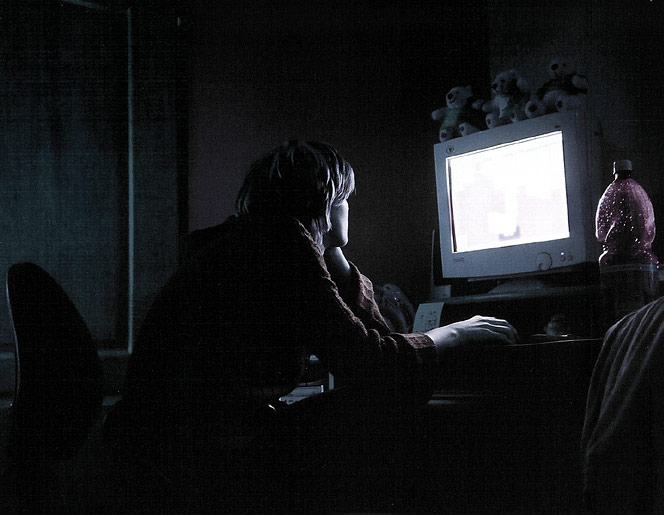
Unseen, unnamed forces are barraging you with lies, and if you weaken and believe them your computer will be turned into a zombie.
No, that’s not a blurb for a bad sci-fi movie—it’s a description of what’s happening on any desktop containing an Internet-connected PC. Before the month is even done, April has set a record for virus e-mails, thanks to a virulent and successful malware called the Storm Virus, Adam Swidler, a manager at Postini Inc., a spam filter service in San Carlos, CA, told LiveScience.
A Storm Virus e-mail carries alarming news blurbs (originally concerning bad weather—hence the name) in its subject line. Clicking on the attached file causes a Trojan to download, installing botnet software that turns your PC into a zombie, placing it under someone else’s remote control.
Security software vendor Symantec Inc. recently reported detecting 63,912 zombies on an average day, and that during the last half of 2006 it detected 6,049,594 separate zombies—29 percent more than during the first half of 2006. (More than a quarter were in China, where computer security is a relatively new topic.)
How it works
In the background, when you may not notice, your computer will begin following the orders of its distant master.
Some zombies get rented out for denial of service attacks, but most send out bulk loads of spam. Some of the spam will contain copies of the virus that enslaved it. (Yes, it’s reproducing.) These days, however, the spam is as likely to tout a particular company, announcing extravagant news that, if true, is certain to drive the stock price of that firm through the roof.
Get the world’s most fascinating discoveries delivered straight to your inbox.
Unfortunately, the news is fiction—the botmaster has picked out a thinly-traded penny stock and has bought a block of shares, sometimes through hijacked online trading accounts. After the barrage of spam goes out, enough gullible people buy shares of the stock to cause its price to move upwards—and the botmaster sells at a profit. The price then crashes, burning those who bought it.
“There’s evidence that some of the people who buy the stock know exactly what’s going on, but figure they can ride the stock price as it goes up and get out when the spammer does,” Swidler said. “But they never can.”
Spam 2.0
This "pump-and-dump" process is a hallmark of what’s also called “Spam 2.0.”
Unlike first-generation spam, which tries to sell something and therefore can be traced to its perpetrator, Spam 2.0 has no obvious link to the source of its funding, making it even more insidious and harder to stop.
In response, the Securities and Exchange Commission has tried temporarily freezing the trading of stocks touted in spam. “But the spammers don’t seem discouraged at all by the SEC’s actions,” observed Swidler. “We have not seen any impact.”
Self-protection, therefore, is paramount. Experts agree on several approaches:
- Don’t open files that are attached to spam, or to any e-mail whose source you are not sure about.
- If your Internet service provider offers spam filtering, use it, or get your own spam filtering software.
- Acquire anti-virus and anti-adware software and keep them updated.
- Use a firewall.
- Since most malware takes advantage of security flaws in the operating system, make sure you have acquired the latest patches. Current versions of Microsoft Windows can do so automatically if there’s a network connection.
And finally, “Don’t respond to any unsolicited offers on the Internet, stock or otherwise,” Swidler urged.

 Live Science Plus
Live Science Plus





