Hardware Security Protects What Software Can't
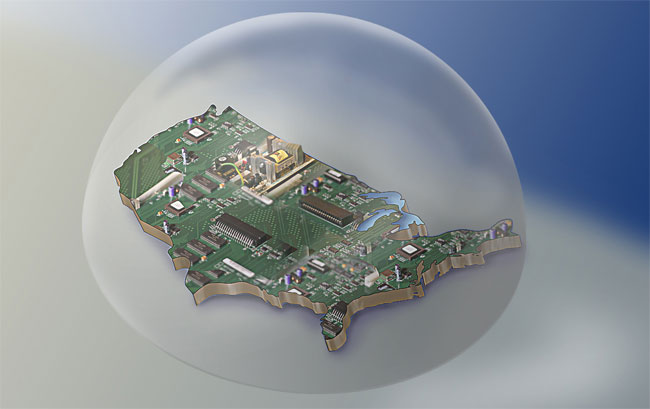
NEW YORK – With advanced malware rendering antivirus software essentially useless, and cloud networks like Gmail putting all of your data eggs in one basket, how can you trust remote servers to keep your info safe? According to Stephen Hanna of Juniper Networks, the answer involves switching from security software to security hardware.
Speaking at the New York Institute of Technology cyber security conference last Wednesday, Hanna detailed how only dedicated security chips can provide the security, and security verification, needed to make cloud computing safe and reliable.
“[With cloud computing], it becomes all the more important to have confidence in the security of those systems. Otherwise, malware can insert itself, and the service on which you are depending becomes unreliable,” Hanna told TechNewsdDaily.
Article continues below“With Gmail, you don’t really know where or how it’s running. You just have to trust that it’s secure. Having hardware security can give you greater confidence in that.”
Unlike security software, which runs on vulnerable multipurpose equipment, hardware security devices are designed for only one purpose. Since these security chips only run a few clearly delineated programs, there’s nowhere for malware to hide, Hanna said.
Not only do these chips protect themselves by shutting down if they detect any activity outside of their original programming, but some, like Trusted Computing Group’s TPM module, even respond to physical stimuli. If the chip senses any drastic changes in electricity flow, fluctuations in temperature or breaches of its physical casing, it erases all of its sensitive data. General purpose hard drives simply can’t match that level of security, Hana said.
“There are so many ways to get your machine infected, and when you move from software to hardware, you take care of the ability of all those viruses to get your security keys,” Hanna said. “Of course, someone could still steal your computer, take it to a lab, and crack it that way, but that’s a spy scenario that’s not likely.”
Get the world’s most fascinating discoveries delivered straight to your inbox.
Most importantly from a trust standpoint, a user can check whether or not a cloud computer uses these security hardware devices. Each hardware security device comes with a digital certificate that is almost impossible to fake, Hanna said. By checking for that digital certificate, a user can rest assured that their data is safe, even if they can’t physically check the computer it’s on.
Thanks to those advantages, security hardware has become a focus of some of the largest computer companies in the world. Last month, chip-giant Intel bought the antivirus company McAfee, a move that signals how interested the market is in this new technology.
This is not to say that hardware security devices are impregnable. In February, computer engineer Christopher Tarnovsky successfully defeated the security on the TPM module. However, Tarnovsky needed far more time and resources to defeat the hardware than he needed to breach even the tightest software security.
This proves that while not perfect, hardware security at least improves upon software enough to inspire confidence.

 Live Science Plus
Live Science Plus