Mind-Controlled Cats?! 6 Incredible Spy Technologies That Are Real

Bond, James Bond

Killer umbrellas, stick-on fingerprints and lock-picking cellphones — James Bond and his nemeses certainly used their share of bizarre spy gadgets over the years.
But many of the most far-out devices seen in old movies have been made obsolete by incredible leaps in today's consumer technology, said Vince Houghton, a historian and curator at the International Spy Museum in Washington, D.C.
"A modern smartphone does more than most people could do 10 years ago on 10 different things," Houghton told Live Science.
Article continues belowFor instance, nowadays, "wires," like those used to catch mobsters plotting on tape, are now entirely wireless, and they're so tiny that they can be concealed in earrings, buttons and even patches under the skin, Houghton said.
And although most of today's cutting-edge spy technology is classified, knowledge of a few bizarre techniques does get leaked. From eavesdropping techniques to programmed kitties, here are some of the most incredible real-world spy technologies.
Cold War-era gadgets

Spying is almost as old as human civilization. Both the ancient Babylonian law called Hammurabi's Code and the Bible's Old Testament described espionage as a way to gain an edge on adversaries, Houghton said. The rise of modern nations, however, caused espionage gadgets to flourish.
During the Cold War, the golden era of James Bond's spy gadgets, a real-life Bulgarian assassin used an umbrella to fire a toxic pellet of the poison ricin into a Soviet defector in London. The Soviets also developed a lipstick gun known as the "kiss of death," which fired a single bullet at close range, Houghton said.
Get the world’s most fascinating discoveries delivered straight to your inbox.
Oops, kitty kitty

During the Cold War era, a few outlandish ideas made it past the drawing board. Unlike animals, which have cochleae in their ears that filter out noise, listening devices were historically bad at filtering out background noise. So, in the 1950s and 1960s, U.S. spies got the bright idea to use an animal's cochlea to spy on the Soviets. They implanted a microphone into a cat's ear canal, a radio transmitter next to the skull, and a battery into its abdomen, and turned its tail into an antenna. Then, they spent hours training it to hop through obstacle courses. Unfortunately for the spies, the high-tech kitty often wandered off in search of food.
"Cats don't really do what you want them to," Houghton said.
So the team went back to the drawing board, retrained the cat to ignore its hunger signals and plopped it down in a park across from the Soviet embassy in Washington, D.C. As soon as it tried to cross the street, it got run over by a taxi.
"They had their multimillion-dollar cat there, smooshed on the street," Houghton said.
For decades, the CIA also spent millions to fund Operation Stargate, which aimed to use psychics to reveal Soviet secrets. The program was disbanded during the Clinton administration. The agency also funded the notorious MKULTRA program, which aimed to harness psychedelic drugs like LSD for mind control, Houghton said.
Visual microphone

The government doesn't develop all the strangest spy technologies.
Scientists at the University of Texas created a way to reconstruct conversations simply by taking pictures of the environment in which the words were spoken, according to a presentation at the 2014 SIGGRAPH conference. The sound spying system takes advantage of the fact that sound waves produce minute, invisible-to-the-naked-eye vibrations that can still be caught on camera. These vibrations can then be analyzed to recreate the original sounds. The new technique now means that, theoretically, anyone who can snap photos or video of a room could recreate conversations that occurred there — without having to bug the place or put their ear to the door.
Hacked medical implants
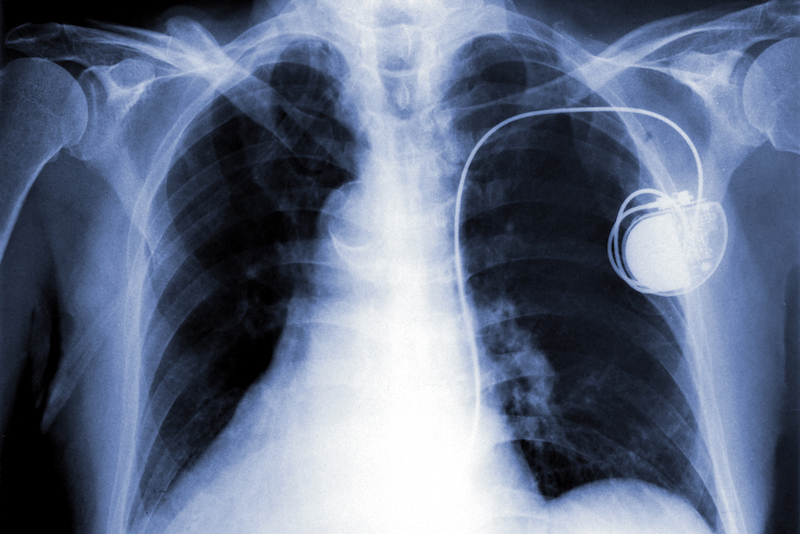
It's not just a plot point on Showtime's "Homeland"; medical devices that can be wirelessly controlled and battery operated — such as insulin pumps, implantable defibrillators and pacemakers — can be hacked. At a 2011 Black Hat Security Conference in Las Vegas, hacker Jerome Radcliffe showed that it was possible to hack his own insulin pump. A few years earlier, hackers raised the possibility that wirelessly controlled pacemakers could also be hacked. So far, no one has documented a case where malicious forces have fiddled with someone's implanted medical device — at least that we know of. But the risk has spurred the U.S. Government Accountability Office, a watchdog agency within the government, to urge the Food and Drug Administration to require the companies that make such medical devices to eliminate these vulnerabilities.
I see you

International spies aren't the only ones who have an interest in watching other people. Companies that want to know more about the people who buy their products could one day use a creepy combination of tailored marketing and surveillance. The company Almax has developed a bionic mannequin called EyeSee that could be placed in clothing stores. Behind the mannequin's dead eyes hides a camera that uses facial-recognition software that can identify a shopper's age, race and gender. The idea is to deduce what kinds of consumers buy certain products.
Unbreakable codes?

Ultimately, the goal of most espionage organizations around the world is to create perfectly secure communications. Some think that quantum encryption — which uses the principles of particle physics to ensure that a message is readable only to its intended recipient — may be the key to creating codes that can't be broken.
"At this point, the [National Security Agency] can listen to anything they want to, regardless of what encryption is used," Houghton said. "Quantum encryption would be the first time you could create a completely unbreakable code."
Today, quantum encryption is still in the proof-of-concept phase, as far as we know. However, the technology is now getting practical enough that governments are probably very interested, he said.
"The first country to pull that off is going to be way ahead of everyone else," Houghton said.

Tia is the editor-in-chief (premium) and was formerly managing editor and senior writer for Live Science. Her work has appeared in Scientific American, Wired.com, Science News and other outlets. She holds a master's degree in bioengineering from the University of Washington, a graduate certificate in science writing from UC Santa Cruz and a bachelor's degree in mechanical engineering from the University of Texas at Austin. Tia was part of a team at the Milwaukee Journal Sentinel that published the Empty Cradles series on preterm births, which won multiple awards, including the 2012 Casey Medal for Meritorious Journalism.