
Cicada 3301: The Mystery Keeping Cryptologists Awake At Night (Op-Ed)

This article was originally published at The Conversation. The publication contributed the article to LiveScience's Expert Voices: Op-Ed & Insights.
Ciphers, conspiracies, secret societies, the dark web - intrigued yet?
Of course you are! As curious animals, there is nothing we love more than a mystery, especially one with a hint of the secret underground. That’s why there’s so much interest in Cicada 3301.
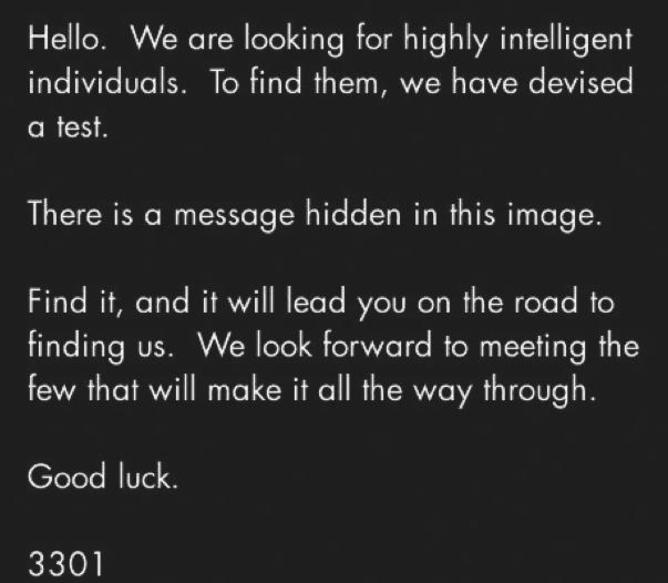
Let’s start with what we know. In early 2012 an image (pictured below) was posted to an internet message board from “Cicada 3301” inviting readers to find a hidden message as part of a search for “intelligent individuals”. Those who succeeded were then led through a series of web-based challenges, closing in on a prize.
Within the pixels of that first image was a clue to the next stage of the scavenger hunt. To see the forest from the trees, you had to spy a reference to Tiberius Claudius Caesar. You also had to know about an ancient encryption method that the emperor used in his correspondence - consistently replacing letters with those further down in the alphabet.
Communities of internet users around the world worked together to solve these challenges, at the close of which some may have been contacted. Nobody is sure whether anyone actually won, but in 2013 the process started again. Once more a series of puzzles were posed and collectively tackled. Successful solvers were approached by email, and then… we just don’t know. Told you it was a mystery!
What everyone wants to know is - who is behind this? As you can imagine, theories are raining in. Some have suggested a recruitment drive for intelligence agencies.
Get the world’s most fascinating discoveries delivered straight to your inbox.
There is past history, from the famous speed crossword puzzle solving tests used to hire codebreakers for Bletchley Park during the Second World War, through to current puzzles being used to recruit for the UK intelligence hub GCHQ.
Others have suggested a big IT company, especially as there is a global element to some of the challenges. Organisations such as Google pride themselves on hiring smart minds capable of lateral thinking, which is exactly what is needed to complete the Cicada 3301 tasks.
A more sinister theory is that this is a membership test for a secret internet society. A dark part of all of us would love this most unlikely of explanations to be true.
And some have suggested that it’s all just for fun – an intellectual game. I am sure those involved are certainly having fun, but this explanation lacks an edge of purpose.
The only clues that we have are the puzzles themselves. It is widely suggested that these require skills in cryptography to solve, but inspection tells us otherwise.
I am reminded of Dan Brown’s Da Vinci Code, a novel that came with its own healthy dose of mysterious secret society. The protagonist, Sophie Neveux, was a cryptographer. Most pleasingly for student recruitment purposes, she was trained here at Royal Holloway, and then had to solve a series of mysterious challenges.
As I have been explaining to schoolchildren for several years, Sophie sadly did not use any of her Royal Holloway cryptographic training in the Da Vinci Code, since the challenges she was set were mainly lateral thinking exercises that required the application of simple codes, general knowledge, or translations from one type of language to another.
The teams of internet users who are tackling Cicada 3301 challenges need almost as little cryptographic training as Sophie. What they primarily need is a very solid set of “hands-on” skills regarding use of internet technologies.
They need to be comfortable with different file formats, internet networking, various messaging environments, and anonymity services. Although they also need a decent general knowledge, particularly of the slightly “nerdy” end of art and literature, the collective community knowledge power being harnessed makes this easier than it would be for a lone solver.
They have to understand a few basic cipher systems to a level of sophistication that anyone on a Crypto 101 course will probably have encountered.
Mathematically, all they really need is to be comfortable with the idea of prime numbers. These are numbers that are divisible only be themselves and one, and come with an association of intrigue because they appear so extensively in nature. Most significantly, the lifecycle of many cicadas tends to be a prime number. So is the number 3301. No coincidence there we suspect.

So who are the people that Cicada 3301 is trying to attract? To put it bluntly, people who are proud to call themselves “geeks”. Cicada 3301 is clearly created for geeks, by geeks. Unless there is a dark underground society devoted to geek status, and let’s not dismiss this at a time when global organised crime is increasingly interested in this area, my best guess is that Cicada 3301 is hiring geeks. But it could also simply be a great celebration of “geekness”.
The latest round of clues is expected to start as early as tomorrow and many cannot wait. Me? I‘ve currently got a job and am not willing to tell you which secret societies I am a paid up member of. Although I am a professional cryptographer, I lack most of the practical skills of geekhood. Off duty, I much prefer tiddlywinks to steganography, so I’ll personally not be paying much attention to Cicada 3301. However, best of luck to all the rest of you.
Keith Martin receives funding from EPSRC.
This article was originally published at The Conversation. Read the original article. The views expressed are those of the author and do not necessarily reflect the views of the publisher. This version of the article was originally published on LiveScience.

 Live Science Plus
Live Science Plus





